Ransomware
Ransomware Attacks
Ransomware can cause devastating damage to individuals, businesses and organisations. This malicious code blocks access to crucial files, with attackers demanding payment in exchange for deactivation codes.
Help protect your business from costly ransomware attacks with simulated testing and expert security awareness training.
What is ransomware?
Ransomware is a type of malware that blocks access to specific areas of the victim’s computer until a ransom is paid.
Unlike most other forms of malware, ransomware usually makes its presence known immediately. Instead of subtly stealing data from an unknowing victim, ransomware leverages fear and panic – demanding payment in return for the malware’s swift deactivation.

How much damage can ransomware cause?
Ransomware attacks are a huge threat to businesses and organisations. A successful attack can lead to crucial data loss, intellectual property theft, and disruption of everyday business operations. This last point, especially, is usually the most costly element of a ransomware attack.
Like other malware types, there is a huge variance in the destructive capability of ransomware. Some variants simply lock the victim’s screen, while others encrypt specific files, restricting access to critical data. Some super-destructive variants (like the GermanWiper ransomware) may even systematically seek out and permanently wipe every data file in a victim’s computer.
Ransomware attackers are almost always seeking instant monetary gain. They’ll usually demand payment in the form of cryptocurrencies like Bitcoin and Monero, which can’t be traced and enable the attacker to conceal their identity.
Anyone with important data stored on their computer or network is at risk, including governments, law enforcement agencies, healthcare systems and other critical infrastructure entities. Crucially, these agencies risk more than just monetary losses.
Ransomware will prevent access to systems or data until a solution is found. If systems are delivering critical services, this can have serious reputational, financial and safety impacts on affected organisations and their customers. For instance, cyber security reports revealed that the infamous WannaCry ransomware attack cost the UK’s NHS more than £92 million – but it also caused over 19,000 medical appointments to be cancelled during the attack period.
Even if the victim has a recent backup of their system, restoring normal operations may take considerable time. Recovery can be a difficult process that may require the services of a reputable (and expensive) data recovery specialist.
Victims of a successful ransomware attack must also consider future implications and the possibility of longer-lasting impacts. For instance, are there more ransomware bugs still present in the system, waiting to be activated? What are they? What will they do? And when?
How does ransomware work?
Most ransomware attacks use social engineering and other phishing methods to trick users into opening authentic-looking email attachments that contain the ransomware. Once installed, the malware begins to encrypt as many of the victim’s files as possible, often extending into any network drives the victim has access to.
When the victim looks for their encrypted files, they’ll then find instructions to pay a ransom if they want to decrypt the locked data.
More recently, ransomware infections have also been caused by unpatched vulnerabilities in software, where simply visiting a malicious website can be enough to infiltrate the network. Data transfers between computers (such as via USB memory sticks) can also cause ransomware to spread, though this is less common.
Though most ransomware strains were originally designed to attack Windows PCs, the rise of BYOD – Bring Your Own Device – means that these days you’ll often also find ransomware hackers targeting Mac computers and handheld devices like smartphones and tablets.
The growth in ransomware attacks
In 2023, the total cost of ransomware attacks is projected to surpass £25 billion.
Since the beginning of 2016, ransomware has been a growing global cyber security threat. The business model for ransomware is incredibly successful and can cause devastating losses to any organisation without appropriate defences.
Previously, ransomware attacks relied on scale to turn a profit – targeting high volumes of vulnerable devices at random. Even by demanding a modest ransom, the sheer number of successful attacks was often enough to make these criminals a decent profit.
Since 2021, however, targeted ransomware attacks have been on the rise, with criminal actors striving to understand the ‘value’ of their targeted organisation before setting a ransom demand based on that perceived value.
In this way, malicious actors aim to cause maximum damage by denying access to business-critical files and systems, and preventing the basic operations of their victim organisation.
Ransomware vs Operating Systems: Windows, macOS & Linux
While ransomware against Windows operating systems has been commonplace for some years, attacks against Mac and Linux systems are also seen.
The methods for infecting systems with ransomware are similar to those used with other types of malicious software, as are the steps organisations can take to protect themselves.
Depending on your level of preparation, ransomware infection can cause wide-scale disruption.
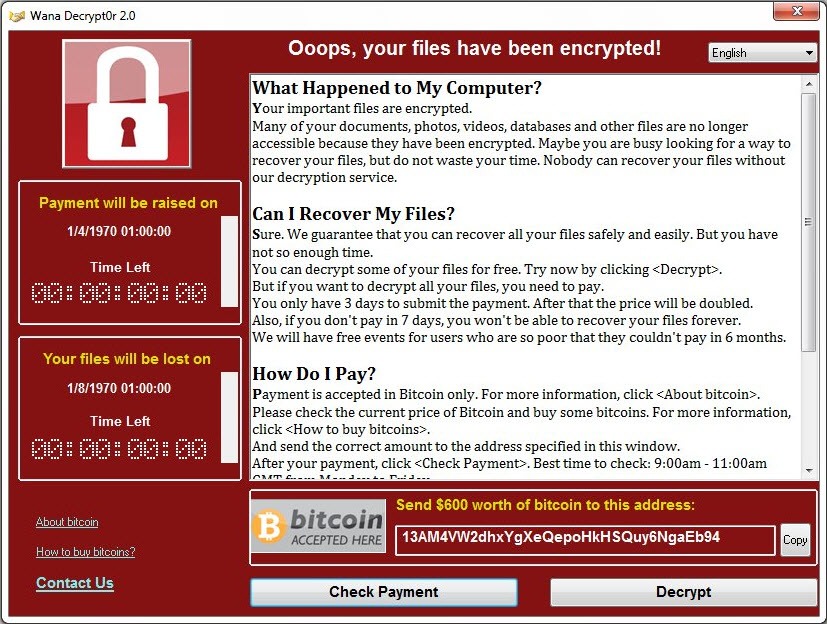
This image is from the worldwide WannaCry ransomware attack, which targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in the cryptocurrency Bitcoin.
It propagated through EternalBlue, an exploit developed by the United States National Security Agency (NSA) for older Windows systems. EternalBlue was stolen and leaked by a group called The Shadow Brokers a few months prior to the attack.
How does ransomware infect your system
Computers are infected with ransomware via a number of routes.
Sometimes users are tricked into running legitimate-looking software programs, which contain the ransomware. These may arrive via authentic-looking email attachments or links to apparently genuine websites (known as phishing).
More recently, ransomware infections have also been caused by unpatched vulnerabilities in software, and simply visiting a malicious website can be enough to cause a problem.
A range of attack vectors have been used, for example vulnerable web browsers, legacy protocols (such as SMBv1) or remote administration tools such as Remote Desktop Protocol (RDP).
Here, attackers have developed methods of identifying and exploiting vulnerable RDP sessions by stealing login credentials and other sensitive information so the use of an SSL VPN tunnel is recommended for all RDP connections.
Other attack vectors are propagated by the use of other malware such as trojans.
Although less common, data transfers between computers (such as via USB memory sticks) can also cause ransomware to spread.
How to prevent ransomware
You can prevent ransomware infections in the same way you prevent any other type of malware infection. Here are some of the methods we recommend:
Defend against phishing
Phishing is a social engineering technique. Impersonating a reputable person or organisation, the attacker manipulates their victim into doing something they shouldn’t – like clicking a malicious link.
By teaching your team about phishing and how to recognise a phishing attempt, you can help protect your organisation from ransomware attacks.
Our Click-Prone® Test is a customisable, simulated phishing test that can help you discover who in your organisation is vulnerable to a phishing attempt. We can then supply a library of expert security awareness training materials to help improve their knowledge, strengthen your defences and protect your business.
Vulnerability management & security patching
Some ransomware strains will exploit software vulnerabilities in operating systems, web browsers, plug-ins or applications to infiltrate your device.
These vulnerabilities have often been announced publicly, with software providers making security patches available to mitigate them. Deploying these patches, or otherwise securing the vulnerabilities, is the most effective way of preventing your systems from being compromised by ransomware.
It’s also important to patch the network systems your devices are connected to, since some ransomware is known to move around networks, encrypting files as it goes. By taking steps to defend the full network, you can prevent an attacker from gaining access to other connected devices.
Control admin privileges & code execution
One common way for attackers to gain code execution on target devices is by tricking users into running macros. You can prevent these attacks from being successful in your organisation by preventing all macros from executing – unless you have explicitly given authority to trust them.
It’s good practice to ensure users do not have full admin privileges and cannot install software on their devices without the authorisation of an administrator.
Remember, however, that some users may sometimes need to run code that you have not pre-authorised. Consider how you will enable them to do this securely, so that they aren’t tempted to do it secretly and unsafely.
Filter web browsing traffic
We recommended using a security appliance or service – such as a firewall – to proxy your outgoing web browsing traffic. You can filter attempted connections based on categorisation or reputation of the websites your users are trying to visit.
Control removable media access
You can help prevent ransomware from being brought into your organisation in an infected USB or other removable media by controlling access to the ports.
3 ways to limit the impact of a ransomware attack
The following measures can all help to limit the impact of a ransomware attack.
Stay in control of user privileges
Compartmentalising user privileges can limit the extent of the malicious encryption.
Make sure you understand the risks brought in by the system administration model your IT architecture uses. Re-evaluate permissions on shared network drives regularly to prevent the spreading of ransomware.
System administrators with high levels of access should also avoid using their admin accounts for email and web browsing.
Limit access on a need-to-use basis
Limit access to your network data and file systems to those who have a business need to use them. This is good practice anyway and, like many of the recommendations made here, prevents against a variety of cyber-attacks.
Backup your data
Organisations should ensure they have fully tested backup solutions in place, with backup files inaccessible to at-risk networks and devices.
However, backups shouldn’t be your only protection against ransomware. Remember that it’s better to prevent than to cure – regular security awareness training and the adoption of good security practices can help stop attacks before they happen.
Ransomware - to pay or not to pay?
Cyber security experts and law enforcement in both the UK and the US all recommend the same thing: do NOT pay a ransom to try and recover your files.
This is for several reasons, including:
- You may not recover your data anyway. There is no guarantee that the criminals will live up to their end of the bargain.
- Your computer may still be secretly infected, causing further issues down the line.
- Your money will be funding further criminal activity.
- Once you’ve shown your hand as someone willing to pay, you are more likely to be targeted again in the future.
This is why it’s crucial to frequently back up your files and store them away from your device networks.
How to report ransomware attacks
If you or your organisation have been the victim of a ransomware attack, you should report it to the National Cyber Security Centre using the form on their website.
No matter the size of your organisation, the severity of the breach or the ransom amount requested – by reporting the attack, you can help fight cybercrime and help prevent further ransomware attempts.
