Worldwide currency exchange Travelex is still offline due to the devastating Sodinokibi ransomware attack, but what can we learn from it?
You may be aware that the foreign exchange giant Travelex suffered a major ransomware attack at the turn of the new year which forced it to immediately shut down all online systems. Across 30 different countries you will see a similar message on their website:
Travelex.co.uk holding page
The disruption Travelex has suffered reverberates through the financial industry, with severe problems at Lloyds, Barclays and Royal Bank of Scotland as their supply of foreign notes (from Travelex) diminishes.
So what caused all these problems, what small bit of malware caused weeks of disruption and millions in lost revenue?
One word: Sodinokibi
What is Sodinokibi?
Sodinokibi, as featured in Phishing Tackle’s list of Top Ten Ransomware Strains, is a form of RaaS (Ransomware as a Service). Also known as REvil, it has gained notoriety through several high-profile attacks over the last year.
Having multiple attack vectors is one of its key strengths, though phishing emails and exploiting known security vulnerabilities (such as Oracle WebLogic) remain its primary methods of infection.
What is RaaS?
This franchise-like deployment method allows hackers with very little coding experience to launch devastating ransomware attacks by simply becoming an “affiliate” to the RaaS service.
Once they are affiliated, the attackers are granted access to the technical documentation, step-by-step instructions to launch a ransomware attack and (in some cases) a platform from which to monitor the attacks progress. Upon successful payment from the target, the ransom is divided between the RaaS provider and the attacker.
Naturally, this method is becoming increasingly popular and perusals across the dark web reveal several adverts for such models.
How does Sodinokibi execute its attack?
Once installed, it connects to a Command and Control server, managed by the attackers, where it downloads several further components. These are placed into system folders and then used to execute a data harvesting module which gathers information about the target system.
The harvested data is then used in the next module, known as “stealth protection”. This scans the system for antivirus and security programs, along with sandbox and virtual environments.
Sodinokibi also alters the Windows registry, allowing it to execute its attack each time the victim powers on their machine. When the attack is executed, it encrypts certain targeted files of varying formats including image, audio and video files, documents and databases along with many others.
After encryption, a random character string is appended to the file extensions of all affected items. Then, at this final stage, the ransom note is delivered, taking various forms, the two most common are below:
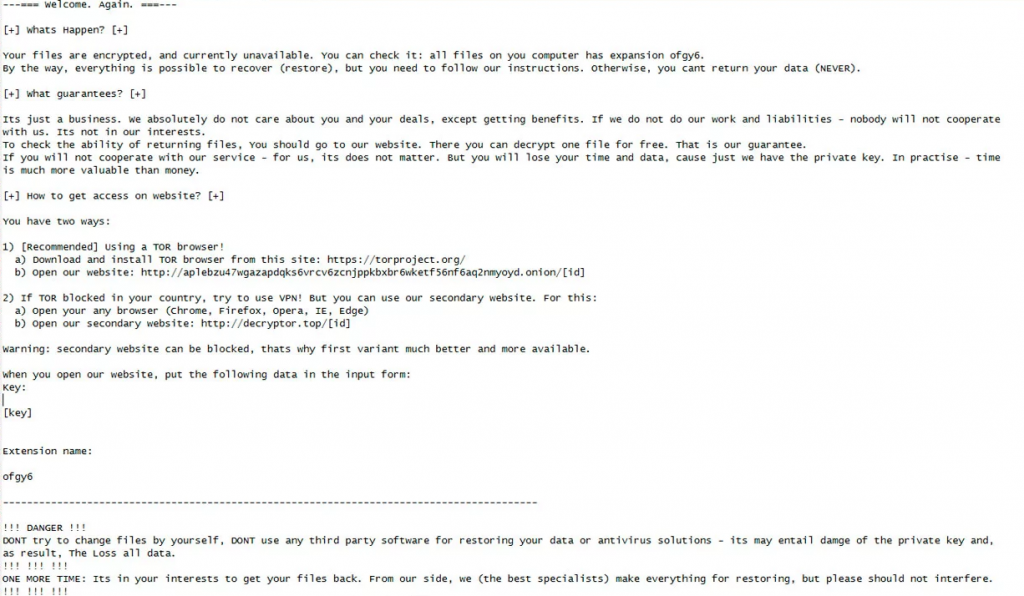
Sodinokibi ransom note…
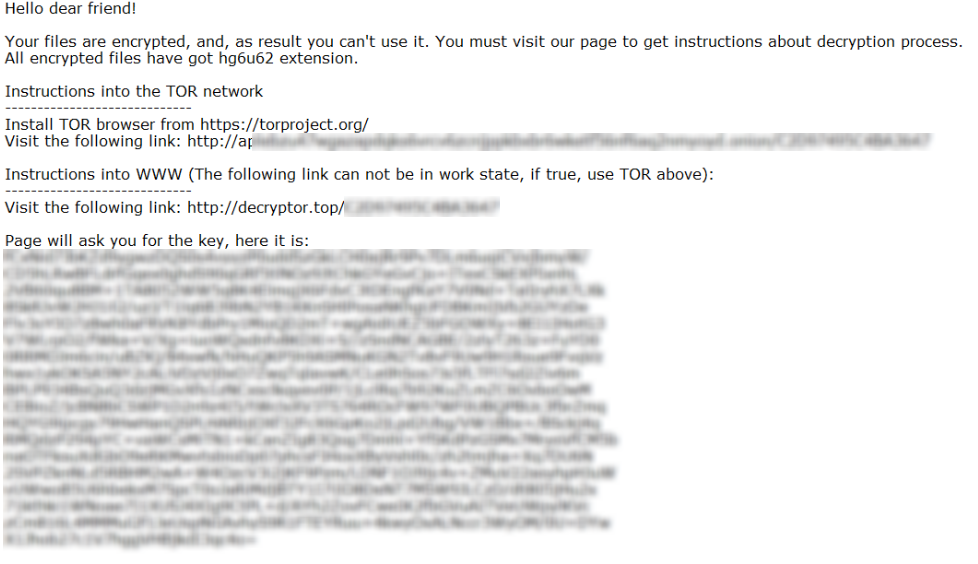
Another Sodinokibi ransom note.
Should the victim visit the site they will be asked for a ransom in Bitcoin, usually $2,500 ($5,000 if they wait more than two days).
How to protect your organisation from a Sodinokibi ransomware attack?
There 3 basic steps you can take to dramatically reduce your chances of falling victim to the Sodinokibi/REvil ransomware strain. They are also relevant to many other ransomware strains and should be observed as a matter of course in any modern organisation.
- Regular Security Awareness Training and Simulated Phishing
- Like many ransomware strains, Sodinokibi is often attached to email-borne attacks, such as spear-phishing campaigns. While advanced security hardware catches some of these attacks, many still get through. When (not if) this happens, the security of the organisation rests entirely in the user’s ability to spot a phishing email.
- Ensure all security software and operating systems are up to date
- Known to exploit known flaws and vulnerabilities in security software, Sodinokibi and other ransomware strains are much more likely to break through old software.
- Remotely back up all vital data
- Keep a disconnected backup which is “encrypted at rest”, use strong unique passwords everywhere, and Two-Factor Authentication (2FA) to avoid further data breaches.
As mentioned above, Security Awareness Training remains the most cost-effective method to reduce an organisation’s cyber attack surface. In reducing users’ susceptibility to clicking on phishing emails (their Click-Prone® Rate), an organisation can quickly, easily and dramatically increase their cyber resilience.
Cyber Security, as with any journey, starts with a single step. To make that first step even easier (and completely free), we created a tool that reveals your users’ current Click-Prone® Rate, check it out here: Free Click-Prone® Test.
No matter the size of your organisation, your cyber attack surface can always be reduced. Find out today how you can reduce yours.








