A new report from Microsoft reveals that not only have spear phishing attacks doubled in the last year, but they have become significantly better targeted as well.
Spear phishing and Business Email Compromise (BEC) attacks are on the rise. The efficacy of the approach is garnered not from the brute-force hacking ability of the malicious actor behind the email, but rather the simplicity and accuracy of the message within which allows them to slip past most firewalls undetected and fool the human victim at the receiving end.
An ethical hacker once likened the approach of BEC as such:
Why try to cut through the door of the vault when you can just ask the guard for the key, you’d be amazed how often they say yes.
Such is the success of these campaigns that BEC has an estimated global cost of £21 billion in the last 3 years.
Because of these spectacular wins (from the scammers perspective), inbound emails associated with phishing have doubled in the last year (between September 2018 and September 2019) as the image below displays:
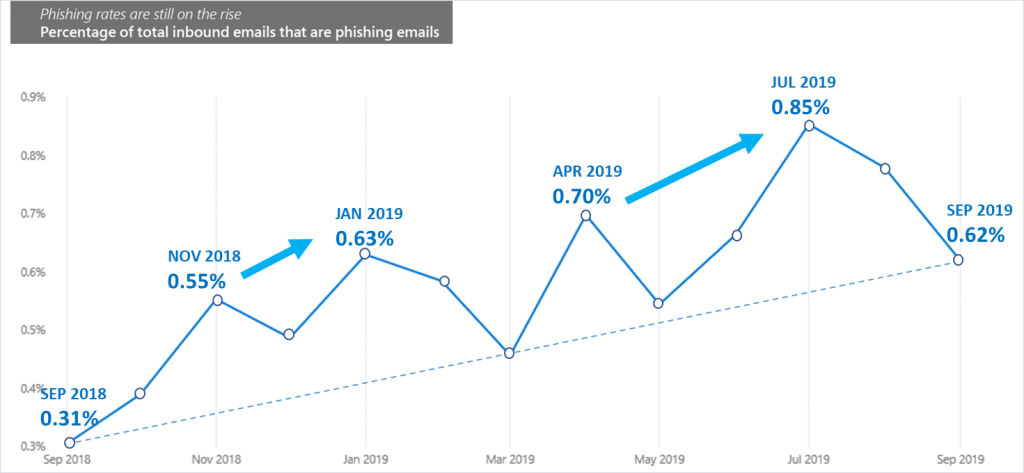
Image courtesy of microsoft
Not only has the quantity of spear phishing and BEC campaigns increased but so has the quality of the emails themselves. Hackers are becoming so adept at targeting the correct victims that Microsoft has coined the term “Laser phishing” instead.
Some examples of Spear Phishing and BEC are illustrated by Microsoft below:
To illustrate how clever some of these campaigns are, imagine a busy recruiter who is responsible for filling several IT positions. The IT director is under a deadline and desperate for good candidates. The recruiter posts the open roles on their social networks asking people to refer leads. A few days later they receive an email from a prospective candidate who describes the role in the email. The recruiter opens the attached resume and inadvertently infects their computer with malware. They have just been duped by a spear phisher.
Now let’s consider a new executive who receives an email late at night from their boss, the CEO. The CEO is on a trip to China meeting with a vendor, and in the email, the CEO references the city they’re in and requests that the executive immediately wire $10,000 to pay the vendor. The executive wants to impress the new boss, so they jump on the request right away.
At Phishing Tackle, we are all too aware of how important regular Security Awareness Training and simulated phishing exercises are (and by regular we mean more than once per month).
As we approach the winter holidays, we too enter the most active period for cyber attacks. We no longer live in a time where one has to wonder if a phishing email will make it into a user’s inbox, it is simply a case of when.
Make sure your users are adequately trained to deal with phishing emails, the success of spear phishing and BEC shows us very clearly that technology alone is not enough to protect your business.
Interested to know how many of your users will click a phishing email? We created a free tool called the Click-Prone® Test which will tell exactly how many of your staff have a propensity for clicking on phishing links.