One of the largest software companies in the world, Software AG, was victim to a “double extortion” ransomware attack this month and has not yet recovered.
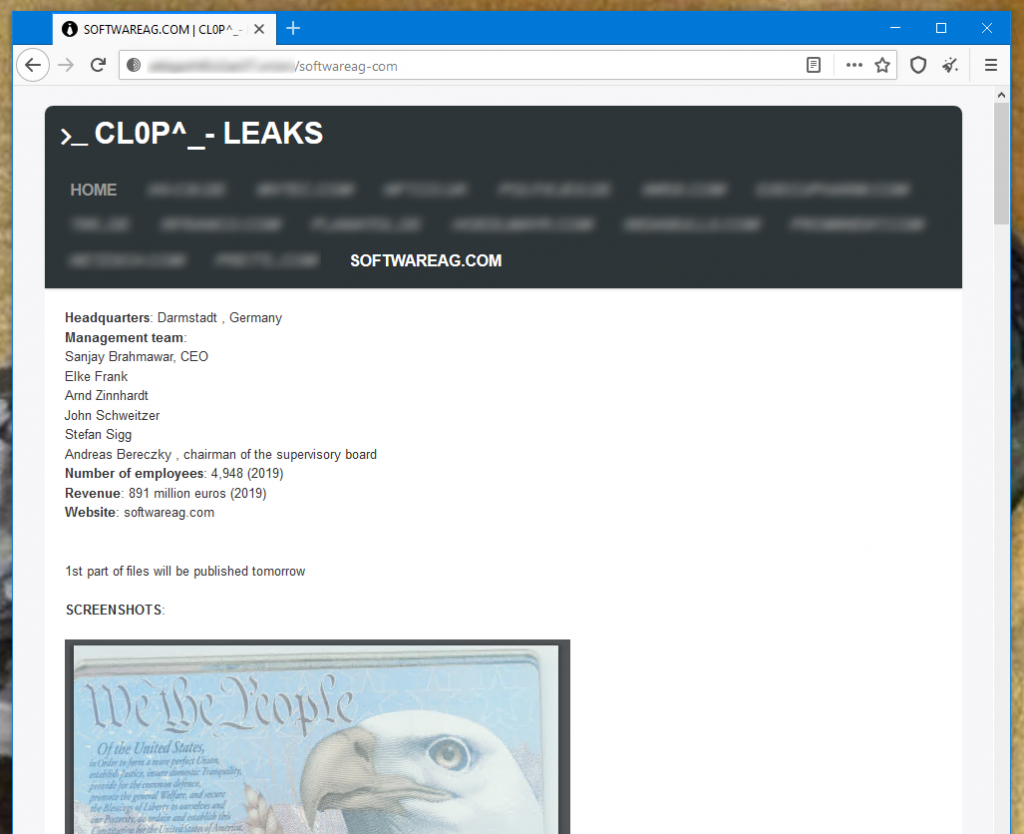
A ransomware gang calling themselves “Clop” were able to break into the company’s network on Saturday the 3rd of October. The ransom demanded by the criminals was $23 million (£17.5 million), one of the largest ever demanded.
After negotiations failed, the gang proceeded to release screenshots of sensitive company data on a website in which the group operate on the dark web. This is what gives the attack its “double extortion” classification, not only do the criminals encrypt the data during the attack, but also export and release the data to the public if negotiations fail.
These screenshots display delicate employee materials, such as passport scans, emails, as well as financial documents and multiple directories taken from the company’s internal server.
The company acknowledged the attack a few days after it occurred when it confessed to having difficulties on its internal network due to a “malware attack”.
Software AG also stated that no customer services had been affected and that they did not know “of any customer information being accessed by the malware attack.” They later contradicted this statement, admitting to have found evidence of data theft. “Today, Software AG has obtained first evidence that data was downloaded from Software AG’s servers and employee notebooks,” the company declared in its follow up statement. “There are still no indications for services to the customers, including the cloud-based services, being disrupted.”
Security research team MalwareHunterTeam discovered a copy of the malware used in this attack against Software AG.
While the original cause is not yet known, many ransomware attacks are the result of carefully planned spear phishing campaigns. When these campaigns are met by carefully trained and tested users, the results of the attack are dramatically different.
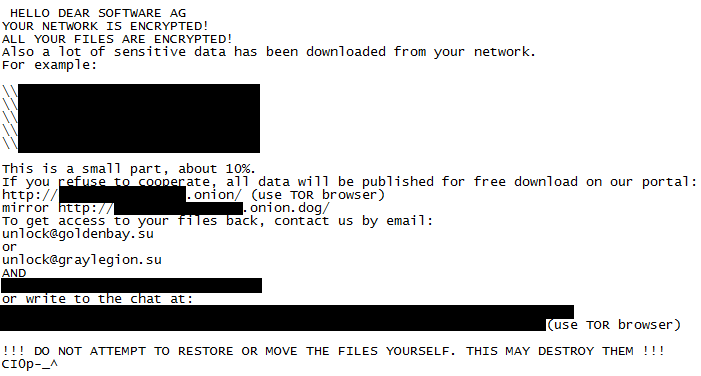
The instructions left in the above image are from the gang, and lead to an online chat room on a web portal managed by the group via TOR browser.
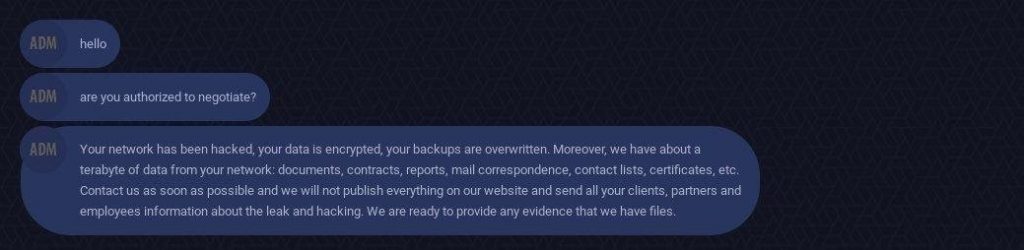
Currently, there is no evidence to suggest that Software AG have paid the mammoth ransom demand.
The company is Germany’s second largest, with customers spanning across 70 different nations. This, if nothing else, highlights the blatant need for more cyber security training across every size and scale of businesses.
Do you need more security training in your organisation? Click here to find out about how many of your users would fall for a phishing attack.