A new ransomware strain by the name of “Snake” is targeting entire business networks, rather than single workstations.
The new strain of ransomware aims to encrypt every device attached to a business network, causing much concern among organisations (and network engineers). While it is not the first strain to utilise this technique (known as “Enterprise Targeting”) it is confirming a larger trend by hackers towards this technique due to the devastating impact it has within organisations.
Other notable strains built around Enterprise Targeting include Ryuk, DoppelPaymer, BitPaymer, Sodinokibi/REvil, Maze, LockerGoga and MegaCortex.
Snake was discovered last week by researchers from MalwareHunterTeam who, along with malware analyst and head of Sentinel Labs Vitali Kremez analysed and worked to reverse-engineer the strain. Kremez also made note of the high levels of obfuscation used in the code.
“The ransomware contains a level of routine obfuscation not previously and typically seen coupled with the targeted approach”
Vitali Kremez – Head of Sentinel Labs
It works by removing the target computer’s Shadow Volume Copies and then shuts down a number of processes related to SCADA systems, virtual machines, industrial control systems, remote management tools, network management software and others. After this, it enacts its signature flourish by way of encrypting the computer’s files (skipping most system folders) and appending a random 5 character string to the file extension (pictured below). It then does this to every connected device on the network.
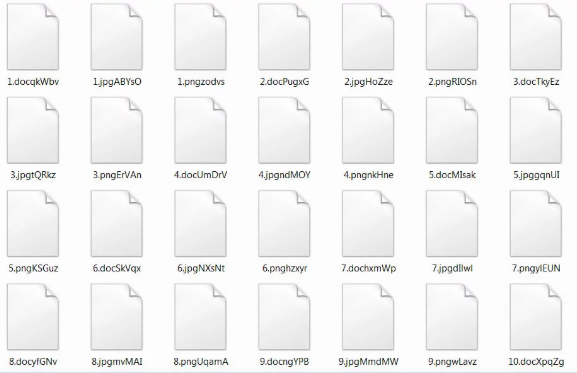
Files encrypted by the Snake ransomware strain.
Once encryption is complete, a note is created on the user’s desktop called “Fix-Your-Files.txt”. The text file describes how your data is now locked with “military grade encryption algorithms” and that you can get them unlocked by purchasing a decryption tool from the hackers by contacting a specific email address. It also mentions that if you send them 3 files (no databases or spreadsheets) they will send them back decrypted as proof of their decryption tools capability.
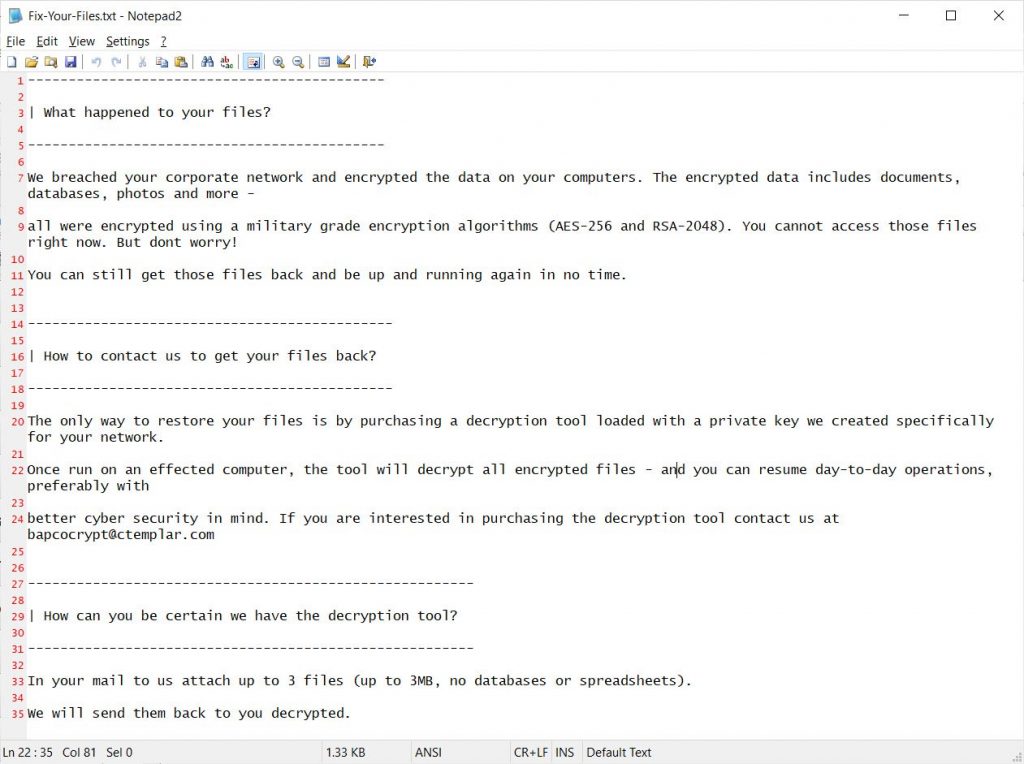
Fix-Your-Files.txt ransom note.
A common and likely route of entry for the Snake ransomware strain is via phishing email, prompting many organisations to seek further training for their staff.
As an integral part of the “People, Process and Technology” security triangle, Security Awareness Training coupled with Simulated Phishing remains the most cost-effective method of reducing an organisation’s cyber attack surface.
At Phishing Tackle, we firmly believe essential education for your staff should not cost the earth. In fact, we went as far as to create a free tool which reveals how many of your staff are susceptible to phishing attacks. Check out our Free Click-Prone® Test and stop guessing as to whether your staff are equipped to deal with phishing emails.
2020 shows no signs that hackers are scaling down their attack efforts, make sure your staff are ready.
Article body images credit: Bleeping Computer