The team behind REvil, number five on our ten most prevalent ransomware strains in 2019 are now using stolen files as leverage for payment from their victims.
For many years, ransomware developers have threatened to release the sensitive data of their victims but have never held true to their promises. Things are changing now, with the recent attacks such as Robbinhood on Baltimore city and Maze on Allied Universal stealing data before encrypting the victims machines to encourage a swift payment.
It doesn’t always work for the hackers, Baltimore never paid them and chose instead to rebuild their systems through restoration and repair. Not only was sensitive data leaked on Twitter, the repair tactic cost the city around $18.2 million. Allied Universal chose also to ignore the malicious actors’ demands and quickly suffered the publishing of 700MB of sensitive data, being told that this was “Only 10% of the total files stolen”.
A representative and one of the few public-facing members of the REvil team by the name of “UNKN” says that large operations will be handled by a newly created “division” within their operation.
UNKN goes on to say the recent attack on the CyrusOne data centre was the handiwork of this new division. The threat now is that if the company does not pay, REvil will release the stolen data to the public or sell it onto the competitors.
The words of UNKN, copied from a Russian hacker/malware forum and translated to English, can be seen below:
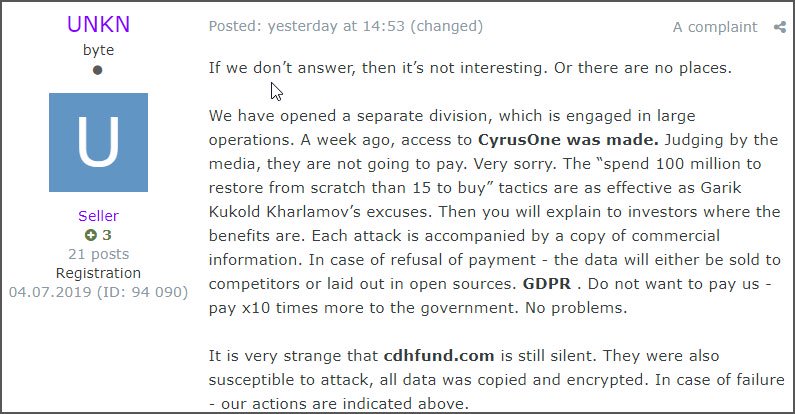
Image credit: Bleepingcomputer.com
One of the largest concerns with this new rising trend is that organisations may start having to treat ransomware attacks as fully fledged data breaches, opening them up to further scrutiny from regulatory authorities such as the UK’s Information Commissioner’s Office (ICO), further increasing the monetary and reputation impact these attacks have.
As a large majority of these attacks are results of successful spear phishing campaigns, the need to educate your organisation’s users on how to spot malicious emails has never been stronger. Up-to-date Security Awareness Training and Simulated Phishing exercises teach your users exactly how to spot phishing attempts and minimise your threat surface in the most cost-effective and efficient method available.
We at Phishing Tackle work hard to provide all our customers with the tools they need to monitor and rectify their users’ susceptibility to phishing emails. We even created several free tools to help all our readers better understand the size of their cyber threat surface.
Have a look at our Free Click-Prone® Test to find out how many of your users are prone to clicking on phishing emails. Also, try out our Free Domain Spoofing Test to see if your domain can be spoofed, a classic attack vector for modern hackers.
As the sun inevitably sets on 2019, so will your organisation inevitably be hit by a phishing attack in the future. It is no longer a case of “if” but purely “when” and when it does happen, make sure your users have the knowledge and skill they need to avoid the sunset of your firm.
Don’t procrastinate, Educate.