Social Engineers have been sending emails masquerading as Microsoft Teams notifications so as to steal user credentials.
The shift towards home working for many users means that malicious actors are working overtime during the COVID-19 pandemic. The rules surrounding cyber hygiene are much easier to follow and police within an office environment than that of the home and scammers know this.
Microsoft Teams, the popular communications and collaboration platform has seen record sign-ups during global lockdown and recent phishing campaigns aims to capitalise on this.
The emails.
The emails (pictured below) come in two forms, both purporting to originate from Microsoft Teams. The first informs the user that an “AudioChat was left” for them and offers a link to view it. The second and more simple message offers several broken images and suggests “A New Files Has Been Shared” with the user which can be viewed in Teams by following a link.
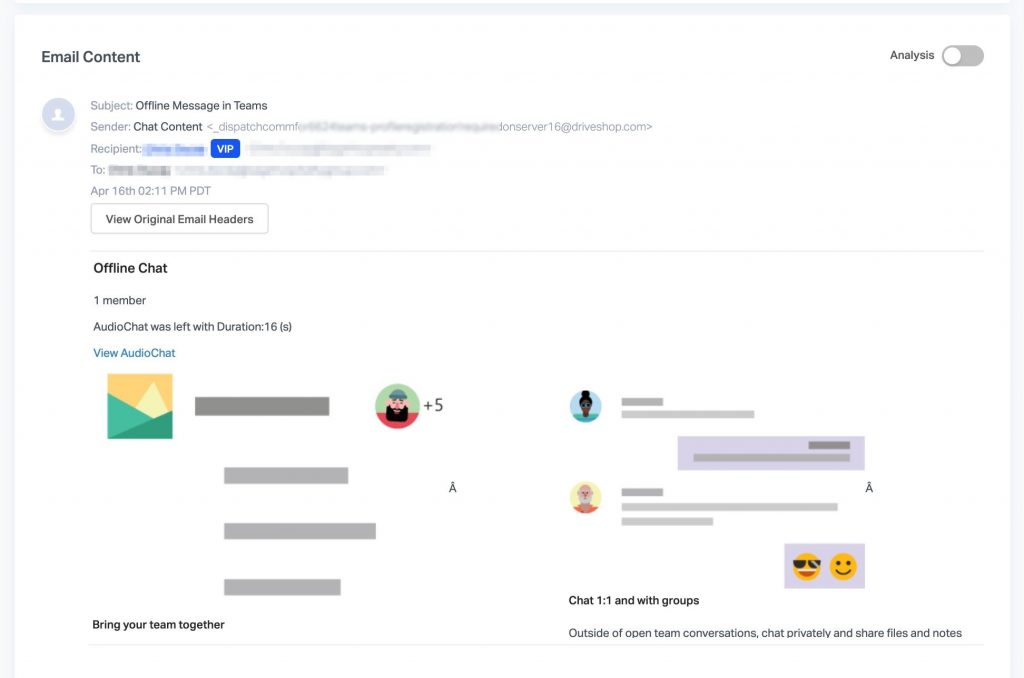
Email 1 – Note the long and unrelated email address, usually a reliable alarm bell that something is wrong.
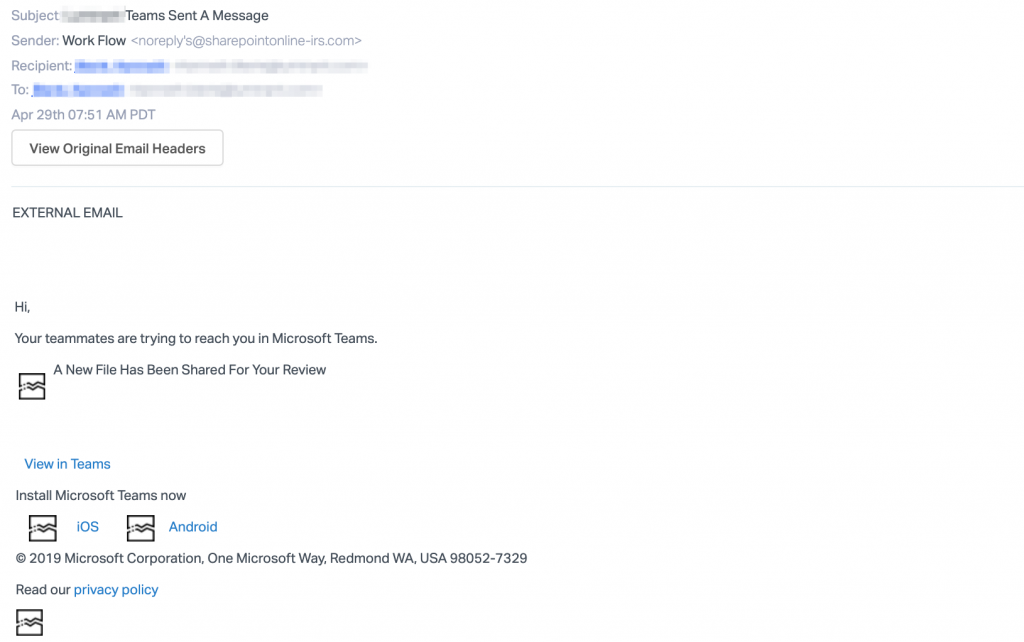
Email 2 – Several broken images would suggest something is wrong, but the mix of domains could be enough to fool unsuspecting users.
The sending address (one of the first things users should check on all emails) used in the first email is very obviously not an official Microsoft domain. The second email, however, has used a clever mix of two correct-seeming domains “Sharepointonline-irs.com“, this is still not an official domain but could well be enough to fool users into believing its legitimacy.
The landing pages.
Each email leads to to its own landing page (pictured below). The first landing page continues the message that someone has left something on Microsoft Teams, while the other landing page veers off entirely to a fake YouTube page asking if the user wishes to leave a certain channel.
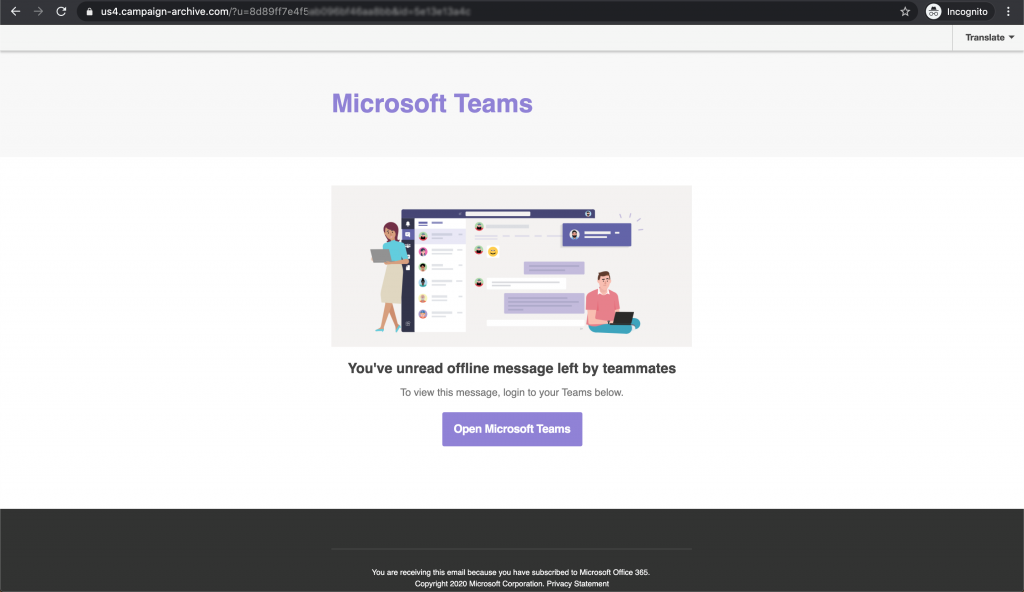
The landing page of the first email, highly convincing if not for the abstract URL.
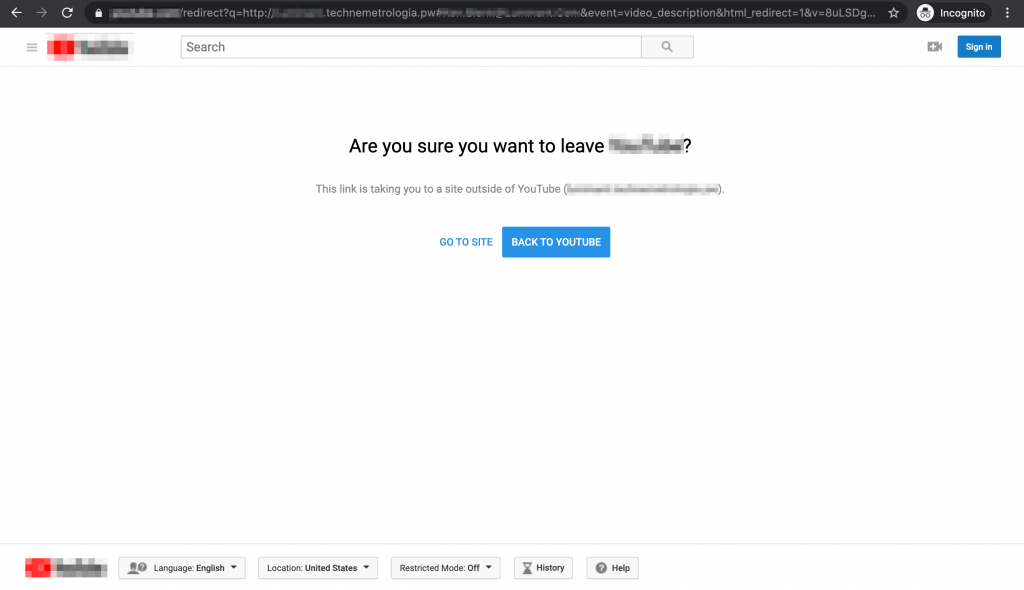
The second email’s landing page, while so many users are working from home, it is not too far a stretch to imagine many users will have a YouTube window open somewhere.
Where both emails work well is on their final landing page (pictured below). While the number of people who fall for the original email may not be high, it is known that there is a 50% chance that users will enter their credentials into a landing page after clicking a phishing email, as we explored in a previous article.
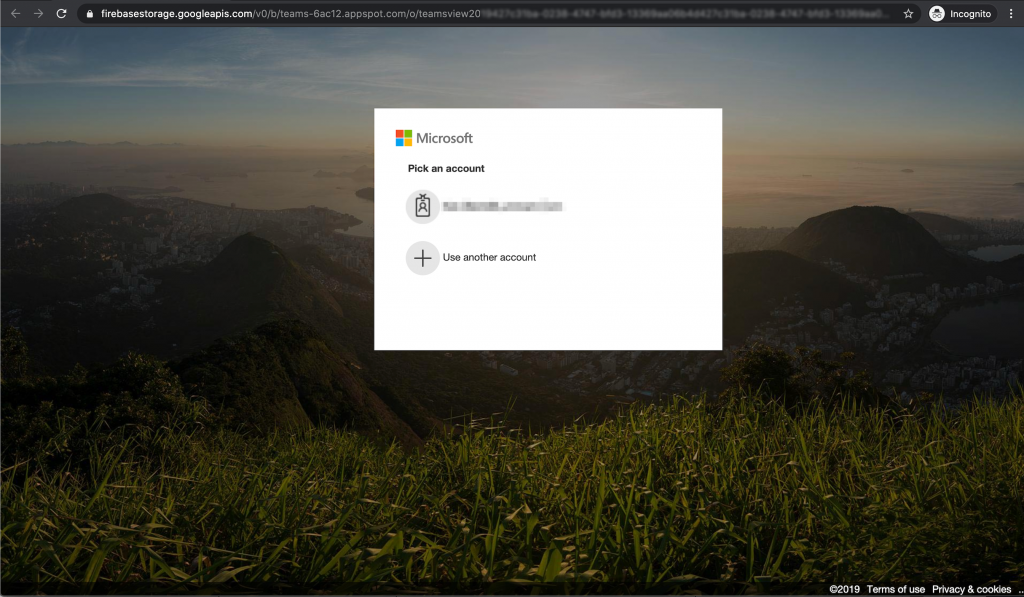
The final landing page of both emails after multiple URL redirects.
What we should learn.
The fact these emails tricked many users into handing over their credentials is a sure sign that organisations must rise to the increased threat posed by malicious actors, especially during lockdown.
Regular security awareness training coupled with regular simulated phishing tests work as the fastest way to boost user cyber awareness and reduce an organisation’s cyber threat surface.
At Phishing Tackle, we’re always updating our list of simulated phishing email templates to include those found in the wild (such as those above) so that our users can be trained on real-world threats.
We encourage all our readers to actively engage in boosting their cyber awareness and understand that the first step is often the hardest to take, as such we’ve created several free tools in order to point you in the right direction. Our Free Click-Prone® Test reveals exactly how many of your users are currently susceptible to falling for a phishing attack and is a fine place to start.
Stay safe.
Email and landing page images credit: AbnormalSecurity.com