A recently discovered phishing campaign is leveraging users’ fear over the recent warnings of an Iranian state-backed cyber attack.
The phishing email appears as a warning from “Microsoft MSA” under the subject of “Email users hit by Iran cyber attack”. It claims that Microsoft servers have been hit by a cyber attack from Iran.
In traditional social engineering style, the hackers attempt to convince the user that they are helping them and says that Microsoft have been forced to lock their account to protect their “Seifty”. The user is then told they must “signin again” in order to gain full access to their data, and is offered a “Restore Data” button at the base of the email.
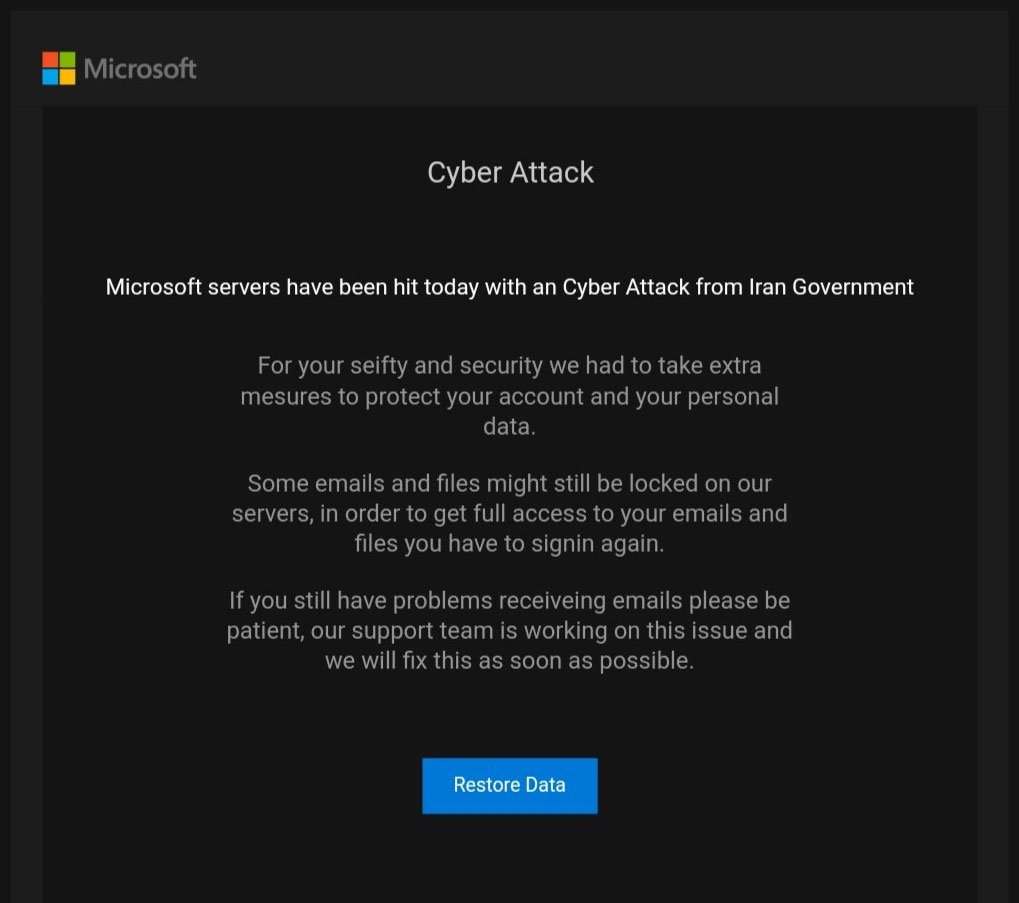
The poorly-written cyber attack email
The sheer volume of spelling mistakes and poor overall structure of the email should be enough to deter any user with a basic grounding in Security Awareness Training. The unfortunate reality is that most users are not regularly trained to spot phishing emails and thus campaigns like these can still cause significant damage.
Should the user click the link, they are taken to a fake Microsoft landing page which imitates the regular login page. Trained users will spot the URL is not even close to an official Microsoft page, however if they have come this far the chances are they are less familiar with phishing attacks and may not even notice the malicious intent.
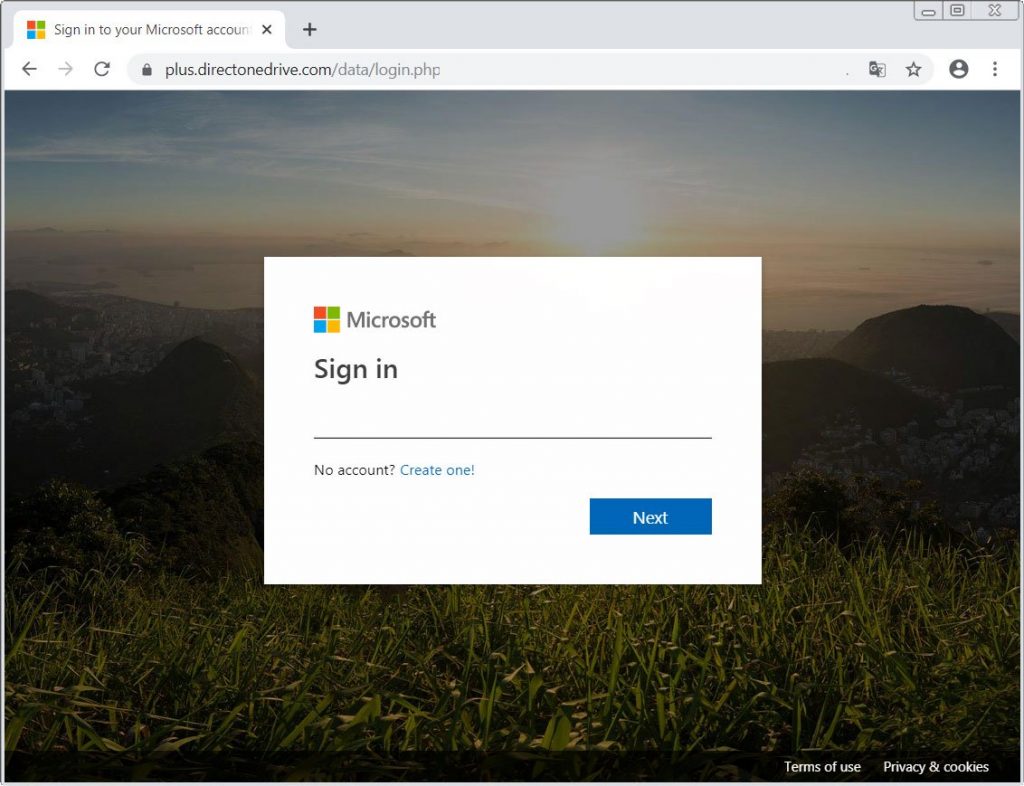
The landing page, notice the false URL
Once the user enters their data it is stored by the hacker for any number of malicious activities, which could range from identity theft to corporate espionage.
The key point here is that without any training at all, users can still fall for even poorly written phishing attempts like these, and inadvertently pose a significant threat to your organisation.
At Phishing Tackle, we even created a free tool which shows how many of your users are susceptible to phishing attacks. Check it out here: Free Click-Prone® Test
Hackers get smarter every day, make sure your users are keeping up with them.
Main article images credit: Bleeping Computer