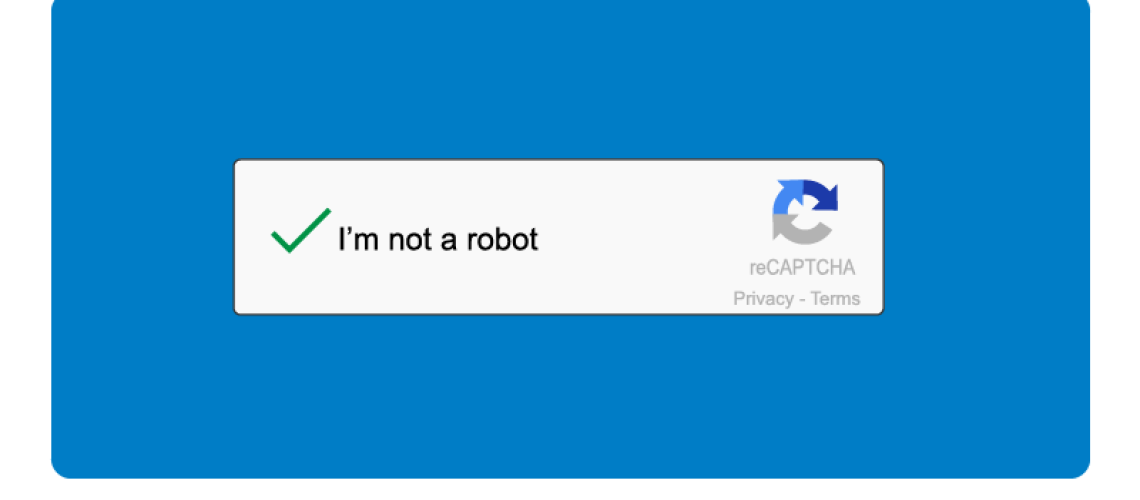
Microsoft users have been targeted in a recent phishing attack, making them the latest victims in the ongoing cyberattack war. The attack uses a fake Google reCAPTCHA system and includes logos of the victim’s companies throughout phishing emails and extremely convincing landing pages to add a solid legitimacy to the appearance. The end goal; steal their Office 365 credentials.
According to researchers, 2,500 of these emails have targeted senior employees in the banking and IT sector throughout the first months of 2021. The emails first take victims to a fake Google reCAPTCHA page, which under normal circumstances is used to secure the website from any abuse or spam in order to tell bots and humans apart. Once this false test is passed by the victim, they are then redirected to a landing page complete with company logos and branding in a bid to steal their Office 365 credentials.
“The attack is notable for its targeted aim at senior business leaders with titles such as Vice President and Managing Director who are likely to have a higher degree of access to sensitive company data. The aim of these campaigns is to steal these victims’ login credentials to allow threat actors access to valuable company assets.”
ThreatLabZ Security Research Team – Zscaler
A slightly different scam, using the same technique has also come to the attention of cyber security researchers. It consists of a phishing email stating that the recipient has received a voicemail from an unspecified sender, and when the attachment within the email is opened, an almost identical fake Google reCAPTCHA screen pops up, and on completion of the test, a message tells the victim that the validation was “successful”.
“After giving the login credentials, the phishing campaign will show a fake message that says ‘Validation successful.’ Users are then shown a recording of a voicemail message that they can play, allowing threat actors to avoid suspicion.”
Victims are then of course asked to input their credentials which are harvested by the attacker. Once saved, the credentials can be used to access the victims’ accounts or sell on the dark web. Should the victim use the same password across multiple online services (as many unfortunately do), the damage potential increases exponentially.
Could all the members of your organisation help to spot the signs of a phishing email and help prevent a potentially devastating attack? Find out in our Free Click-Prone® Test today