Security with a scam
A recent phishing campaign is targeting Instagram users with a false login attempt warning and using fake 2FA codes to appear legitimate.
Login attempt emails are nothing new to the phishing scene, the urgency and perceived sense of danger often makes them an ideal choice for scammers.
Whilst not a perfect solution, the current cyber security best-practice from the UK’s National Cyber Security Centre recommends the use of 2FA to largely mitigate malicious logins. A recent study by Google suggests that using 2FA can prevent as much as 99% of bulk phishing attacks and from our experience with working with ethical hackers, we know it’s a real barrier for them.
2FA can help protect your online accounts, even if your password is stolen
UK National Cyber Security Centre
But what to do when a malicious email gives you the impression that you are using the most secure methodology?
This is the exact tactic used within this new campaign, in which the recipient receives an email saying their account has been potentially compromised and they must enter (what appears to be) a one-time password (OTP) to secure it.
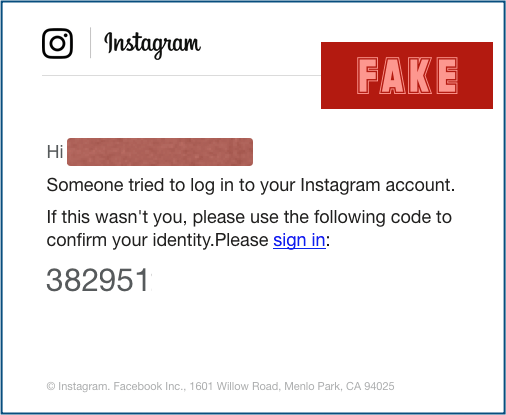
“Someone tried to log in to your Instagram account. If this wasn’t you, please use the following code to confirm your identity”, the email states, giving a 6 digit code for the recipient to enter on what looks to be a real login page.
This is very clever, it gives the recipient a false sense of security by making them think they are adding further security to their account, when in truth they are doing the exact opposite.
By leveraging both the fear of a personal data breach and the apparent security of 2FA, this email is seeing remarkable success, an A for effort to this hacker.
Close, but no cigar
There are, however, a few alarm bells which can be spotted by examining the fake Instagram login against the real one…
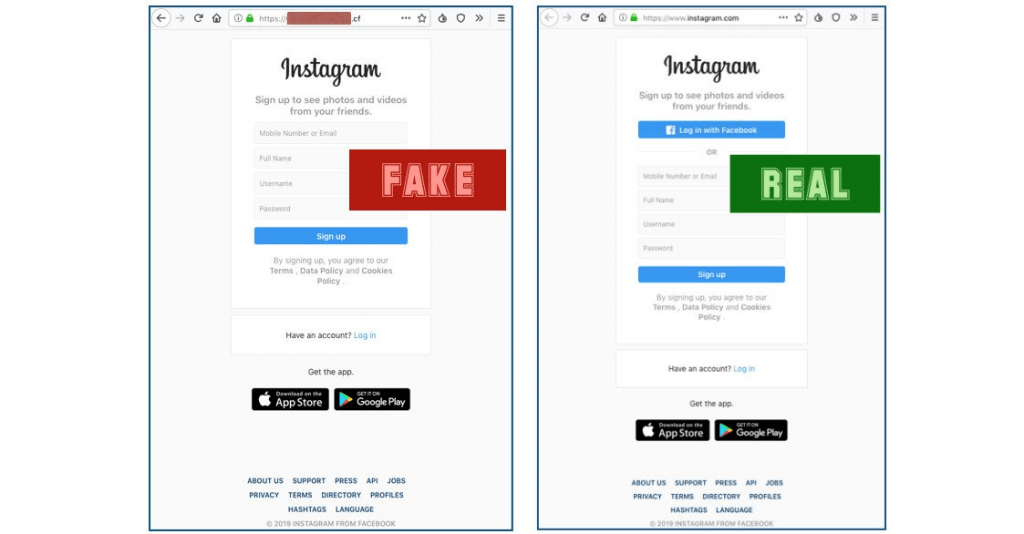
- The most obvious, (for those who check) the URL is not even close to the Instagram login page. We have removed the body of it for security reasons but the “.CF” top-level domain from the Central African Republic should be enough to deter anyone who looks.
- The ‘Log in with Facebook’ link is missing completely. Instagram, being part of the Facebook group will always give you the option to log in with Facebook.
- WHERE DO I PUT THE 6 DIGIT CODE? This may seem trivial but it is vitally important when spotting scams. The hacker has specifically told you to enter a code, yet given no obvious place to enter it.
How NOT to fall for it, 4 useful tips
I’m happy to admit that the above example was pretty well executed (OK, I’m not happy about it but I’ll still admit it). Given the effort put into this and many similar campaigns it’s understandable that hackers are still tricking many victims.
Here are 4 tips on how to avoid falling for these campaigns in the future:
- Email sign-in links. DON’T. CLICK. THEM. Unless you have specifically requested an account verification email, there is almost never a need to sign in from an email link. If you want to check the activity on your account, just sign in from the regular website. For added speed, bookmark the page so you don’t even need to type the whole address in every time.
- Check the URL. ALWAYS check the URL, if it doesn’t look right, just close the tab and move on. Just because it says HTTPS and shows a secure padlock DOES NOT mean it’s a safe website. In fact, with the latest version of Chrome and other browsers, you don’t even see the HTTPS As many as 58% of phishing domains use HTTPS to add authenticity, so don’t assume it’s the real thing without checking.
- Stop panicking and think. Phishers notoriously use scare tactics (like breached account warnings or imminent danger if links aren’t clicked) but before clicking anything, ask yourself if it is actually relevant to you. At Phishing Tackle, we have seen recipients falling for Gmail password change requests when they don’t even use Gmail! Think carefully if the email is just baiting you for a swift response before clicking anything.
- Educate, don’t procrastinate. Security awareness training (SAT) is the most effective method (in both cost and practice) of reducing an organisation’s susceptibility to successful phishing attacks. If your organisation doesn’t offer SAT to it’s staff, it should and it should do it fast.