Phishing Tackle takes a look at 10 interesting cyber security statistics relevant in 2020 to all internet users (professional or otherwise).
The relative importance of statistics is something many readers find somewhat subjective. While a statistic on Spear Phishing may be of particular interest to the CISO of a large bank, the head of IT for a healthcare trust may be far more interested in statistics on ransomware.
This being the case, our list compiled below is not meant to be in order of ascending or descending importance, it is a list of cyber security facts we find interesting and believe to be important enough to take note of.
So let’s dive straight into it!
Phishing Tackle’s list of 10 interesting and useful cyber security statistics in 2020
1 – Google blocks more than 18 million COVID-19 themed phishing emails every day.
Firstly, we apologise for bringing the subject back to the coronavirus pandemic which currently dominates all headlines and conversations.
Google has been working especially hard during the lockdown to keep the swathe of new phishing emails at bay. Just last month the number of coronavirus themed phishing attacks grew by 667%, and the tech giant claims it blocks around 18 million of these each day to its Gmail users.
In case you were wondering, that figure only includes phishing emails, Google blocks another 240 million COVID-19 spam emails each day as well.
While this does sound like a lot, when measured against the 3.4 billion phishing emails sent across the globe every day, there are still an enormous quantity of emails making it through security and into the end-users inbox.
2 – 94% of malware is delivered by email.
Social engineers are endlessly trying new ways to breach network security, and email is by far and away the most effective method.
Over 90% of data breaches are caused by end users clicking on phishing emails, and as scammers get better at fooling those users, so the necessity for training how to spot phishing emails grows.
3 – A new phishing site is launched every 10 seconds.
Stealing user credentials is what the majority of phishing campaigns aim to do (as you’ll see further down the list). By fooling users into thinking they’re entering their details into authentic websites, hackers can build huge databases of stolen information.
Internet users must be more alert than ever before as they traverse their favourite pages, checking carefully every URL they visit and treat all suspicious pages with extreme prejudice.
4 – 68% of all phishing websites use HTTPS.
There was once a time where you could quickly spot the authenticity of a website with that lovely little padlock next to the URL. Unfortunately, those days are long gone as the majority of phishing sites use HTTPS encryption with a valid SSL certificate.
What this means for end-users is they must become more skilled at being able to spot the subtle differences which give away many fake websites. This can be accomplished with regular security awareness training which all organisations should provide as protection of their own interests. Of course the lessons learned by the user can then trickle into their personal lives which helps build security-first cultures inside and outside of the office.
5 – Spear phishing emails are the most popular infection vector.
As internet users have become more savvy at spotting generic spray-and-pray phishing attacks, so hackers have turned their attention towards more targeted and well-researched campaigns.
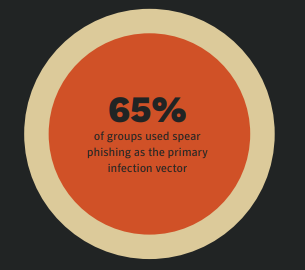
This trend has also made it harder for email security hardware and software to catch these malicious emails as they often mimic the wording and structure of a target’s commonly received emails.
Image credit: Symantec
6 – Human intelligence, user knowledge, is the best defence against phishing attacks.
There is still no viable security hardware/software combination that can block 100% of phishing emails from reaching a user’s inbox.
This means that it is not a case of “if” but rather “when” a phishing email makes it through, the security of the entire organisation rests on the knowledge that user has and their ability to spot phishing emails.
For this reason security awareness training coupled with simulated phishing tests is (by no small margin) the most cost-effective method of reducing an organisation’s threat surface.
7 – 74% of phishing attacks harvest user credentials.
As mentioned earlier, the vast majority of phishing attacks go after user credentials. In the hands of a tenacious hacker a set of credentials can be a versatile tool, used to sell on in large databases or individually, or to lock users out of their own accounts and access their personal/financial information.
The relative ease with which they can be harvested makes them an obvious goal for most campaigns.
8 – 84% of SMBs are targeted by phishing attacks.
California-based network security specialist Untagle Inc. recently reported that 84% of Small to Medium Businesses (SMBs) had been targeted by phishing attacks.
This reinforces the notion that organisations of all sizes must treat their email security extremely seriously, scammers will go after anything they believe they can likely get.
A relatively common misconception is that if an organisation is not “too big” they will be ignored by hackers but this is simply not the case.
9 – SaaS/Webmail remain the most targeted sectors by phishers.
During the final quarter of 2019, organisational protection agency OpSec Security found that Security-as-a-Service and webmail sites remained the most frequently targeted by phishers, as below:
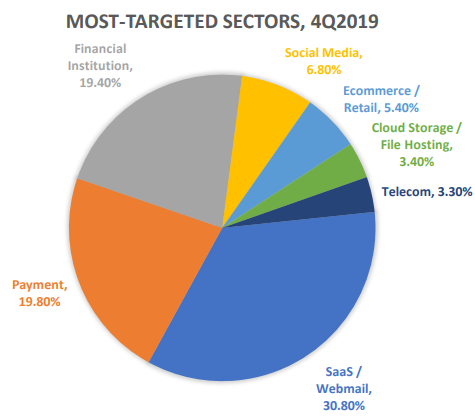
Image source: AWPG
10 – Gift cards are the most common BEC cash-out method.
Business Email Compromise (BEC) attacks target employees with access to an organisation’s finances. Usually impersonating a higher-ranking employee (often the CEO) they try to trick the employee into sending them money.
Email security specialists Agari found that a large majority of BEC cases requested the victim send gift cards over direct wire transfers.
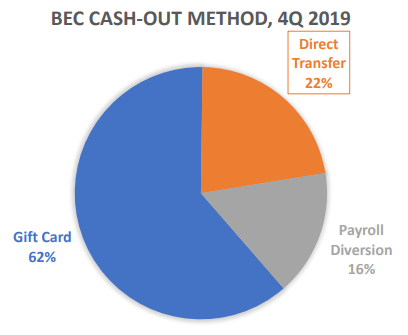
Image source: AWPG
These statistics remind us that user knowledge has to increase in order to ensure the security of an organisation.
Phishing emails and similar scams continue to increase and without regular training, users run the risk of damaging or even destroying their organisation.
The time to educate is now.
Main image adapted from freepik.com