You’re invited to the spam party!
Calendar Spamming!
Hackers use as many tricks as they can to get you to click on malicious links. With techniques such as “spray and pray” phishing, spear phishing and CEO fraud being very popular at the moment.
A recent addition to this list is “calendar spamming”.
This technique works by adding a fake event to the victim’s calendar and enticing them to click on a link within the event. The social engineer behind the attack will often use vague but intriguing terminology to pique one’s interest, headlines like “Your new phone is ready for collection”, “Urgent appointment” or “free giveaway” are all commonplace in calendar spamming.
These nefarious events specifically target users of calendar apps from Apple, Google and Microsoft, and with good reason (we’ll come to that bit later).

A tried and tested approach
Within these calendar invites are a myriad of attractive propositions leading the potential victim to click the link within. Not every one of them is a malicious attack, but they all fit snugly into the “Spam” category. Some examples include traditional ads, pharmaceutical offers, pornography, debt reduction or “get your money back” promises, time-limited free products, and (more nefarious) phishing and malware links.
At Phishing Tackle, we have already been asked us if their calendar app has been hacked after noticing unwelcome invitations within their agendas.
The reality here is that none of them have been hacked, in fact, their calendar app was functioning exactly as it was supposed to.
In an effort to create a more streamlined user experience Apple, Google and Microsoft calendars all accept invitations to events sent via email by default. One can certainly understand why this is a feature and it is a shame that malicious actors make it necessary to remove this automation. So far, only Google has confirmed that they are working on the issue.
What can I do about it?
Here are a few steps you can take to reduce your susceptibility to this unwanted – and sometimes malicious – calendar-clogging spam.
Apple Calendar
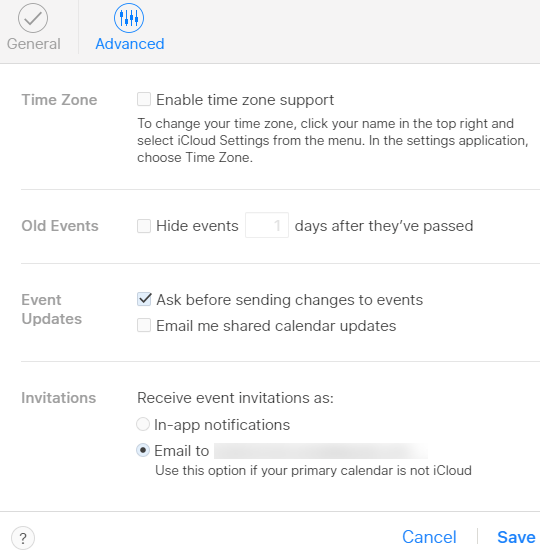
- Click the gear icon towards the bottom left of the Calendar screen and select “Preferences.”
- On the box that appears, click “Advanced.“
- Next to “Invitations“, check “Email to [your email]”
Google Calendar
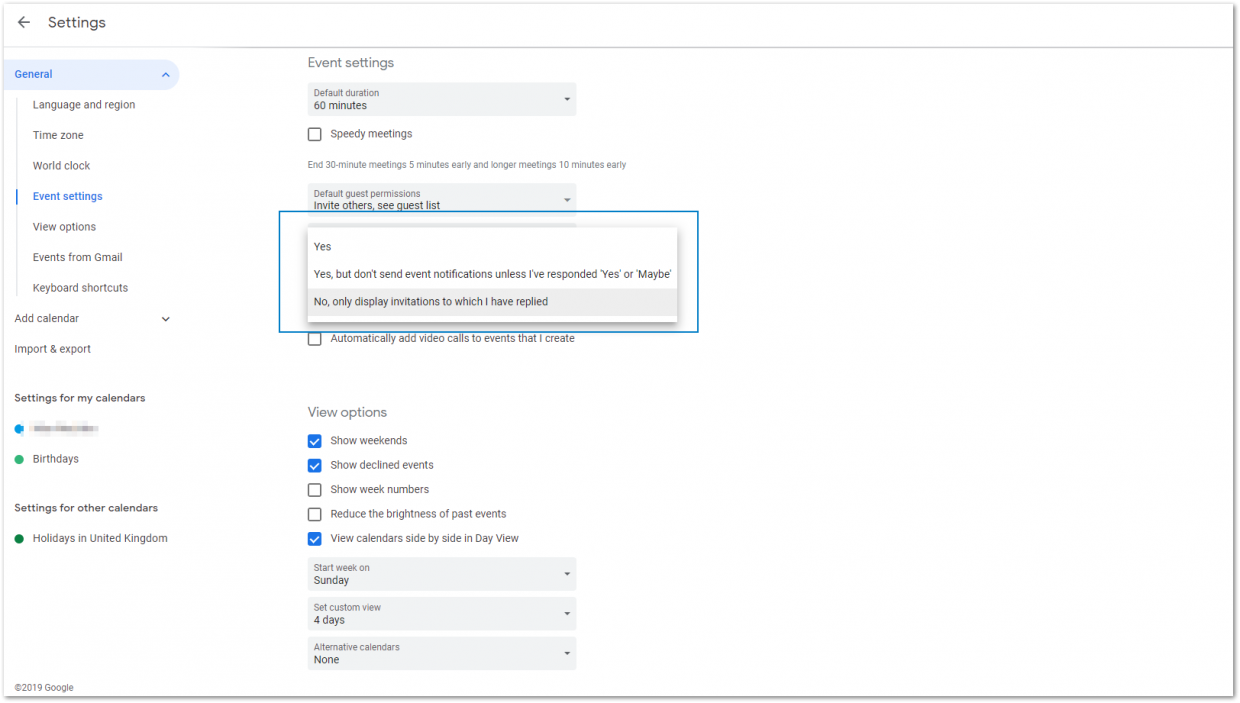
- Click the gear icon towards the top right corner of the main calendar screen.
- Hit “Settings“.
- On the left dropdown menu, hit “Event settings“, under “General“.
- Click the dropdown box titled “Always add invitations” and select “No, only display invitations to which i have replied.”
Microsoft Calendar (Via Web/Outlook Web Access)

- Click the gear icon in the upper-right section of the screen.
- Hit “View all Outlook settings.”
- Hit “Calendar.”
- Hit “Events from email.”
- Underneath “Add these events to my calendar from emails:” change all the settings to “Only show event summaries in email.”
3 Further precautions…
Naturally, by changing these settings it means you will have to manually accept non-malicious/spam invite requests, such as those from hotels, dinner reservations etc… Though this does add a little legwork, it activates and strengthens one of the most powerful tools we have, user engagement.
Below are 3 steps that you can take to boost your own engagement and that of your colleagues.
- Always check before you click. Hover over URLs and check where they actually redirect to.
- Treat unknown emails and calendar entries with extreme prejudice. If it looks suspicious, don’t hope for the best, take action and remove it.
- Take part in regular Security Awareness Training. This has been proven to be one of the most cost-effective methods of risk-reduction.
For further reading on boosting your online security, check out this post by the UK’s National Cyber Security Centre (NCSC): https://www.ncsc.gov.uk/collection/top-tips-for-staying-secure-online
While all of these steps may seem like a pain, they pale in comparison to the financial loss and psychological trauma caused by a successful data breach.
Follow the guidelines above and you have added yet another layer to your human firewall.
Stay vigilant, stay secure!

