This latest phishing campaign is a very convincing attempt at harvesting Amazon user credentials. The hackers are using phishing emails disguised as an Amazon AWS account suspension notice to try and trick victims.
Trust and professionalism are two key ingredients in a successful phishing attack. Most of us know and recognise big companies like Amazon, Microsoft and Apple, so social engineers often masquerade as large organisations as a way to build trust.
What is the AWS phishing scam?
The AWS phishing scam goes down the tried-and-tested route of making victims believe that if they don’t take action, they will lose access to an essential service.
In this case, Amazon Web Services (AWS) is one of the world’s largest cloud computing companies in the world. The service has more than 1 million active users, ranging from small local businesses to global enterprises.
The phishing email is simple and pretty convincing: it states that the victim’s AWS account has been suspended due to an outstanding bill and can be reactivated by clicking the “payment page” link and following the payment instructions.
This malicious link, however, takes the victim to a fake AWS login page that harvests their Amazon credentials and shares them with the hacker.
How to spot a fake AWS email
The fake Amazon spoof email and landing page are very well put together, but there are still some clear signs that give the hacker’s game away.
Although the phishing email is convincingly written and uses a few clever techniques, they aren’t perfect.
Take a look at this image of the initial email.
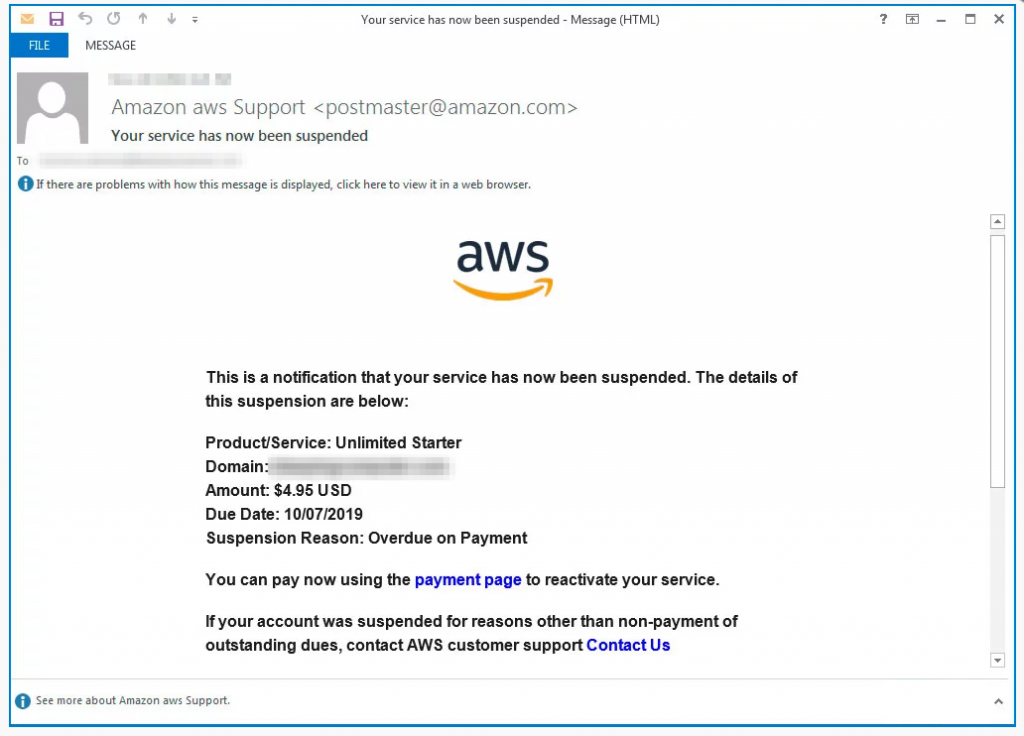
The phishing email, claiming to be from Amazon Web Services
Suspicious sender name
The email claims to be from “Amazon aws Support”, which raises a few red flags.
“AWS” stands for “Amazon Web Services”, which would mean the email account is registered to “Amazon Amazon Web Services”. Obviously, this makes no sense.
Secondly, logo design apart, Amazon use a capitalised AWS in all official literature, so “aws” is also incorrect.
Domain spoofing
The email uses the domain “amazon.com” which, although convincing, is NOT a clear sign that this is a legitimate email.
This is called domain spoofing and is incredibly common in phishing emails. In fact, it’s so common that we created a free Domain Spoofing Test so you can test your organisation’s security settings. It’s important to check whether your system can spot when an attacker tries to spoof your domain.
Grammar mistakes
Another subtle-yet-clear sign that this is a phishing email is the language used. Pay attention to how they explain why the account is suspended:
“Suspension Reason: Overdue on Payment”
This is not correct English. The final sentence doesn’t make sense either, as it asks the user to click “Contact Us” if their account was suspended for other reasons. Think about it: Amazon wouldn’t suspend your account and send an email saying you’d missed a payment, unless you actually had missed the payment!
No SSL certificate
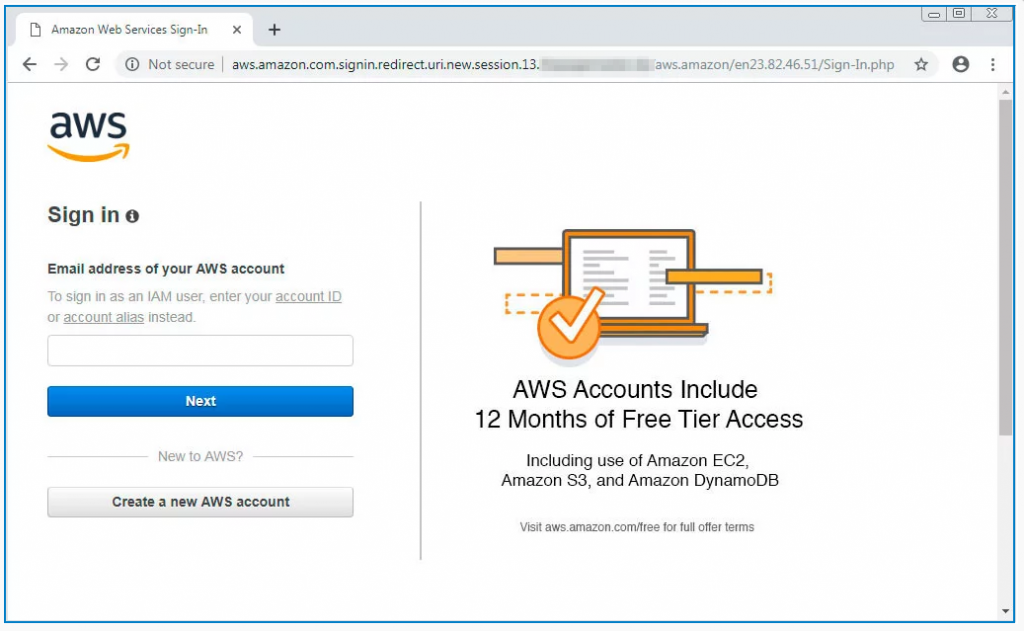
If a victim did fall for the email and click any of the links, they would be taken to the landing page above.
The page itself is nicely laid out and looks relatively legitimate but the key red flag here is the URL:
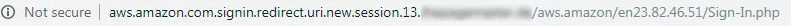
Note the “Not secure” warning at the start of the web address.
This is very poor show from the hacker. AWS generates around $30 billion a year in revenue and it’s highly unlikely that Amazon would forget to HTTPS-protect their login page.
Dodgy URL
The URL contains “amazon.com” which is often all it takes to convince many phishing victims.
However, it doesn’t end there. If you carry on reading the website address, it continues with “.signin.redirect.uri.new.session.13” – and much more!
This is NOT a real Amazon domain. If the URL doesn’t seem right, proceed with extreme caution.
What to do if you receive an AWS phishing email?
If you receive a suspicious email claiming to be from Amazon or AWS, you can submit a report on Amazon’s AWS website. You can also forward phishing emails directly to stop-spoofing@amazon.com.
If a victim misses the red flags and enters their credentials, the hacker saves their details and redirects the user to the real login page. This is a standard practice for hackers, who want their victims to remain unsuspicious for as long as possible.
If you suspect you have already been scammed, you can find more information on how to proceed from the Citizens Advice Bureau.
How to protect your company from phishing scams
Training and educational materials are the best way to ensure your employees know how to avoid falling for phishing attacks like this one.
Security Awareness Training makes it easier for people to spot basic red flags, and with regular simulated testing, you can ensure your business is better protected from cyber attacks.
Book your free Phishing Tackle demo today.








