Often the words “cyber criminal” and “computer hacker” conjure up images of people in dark rooms typing endless streams of code. Perhaps they are in an underground or hidden location, with security cameras covering all entrances. All we know is they won’t stop typing until they finally gain access to vital codes or find their way into the ambiguous (and far too often eluded to) “Mainframe”.
The idea of hackers breaking into computers using this “mash the keyboard till I break their security” approach has been encouraged in mainstream media for decades. While there is a shred of reality that can be found in some of Hollywood’s finest hacking scenes*, just like most other things off-screen, the reality is far less exciting.
In fact, the reality is that most common phishing attacks (around 99% of them!) rely on what has proven year after year to be the weakest link in the cyber security chain: User error.
A recent 18 month study showed that 99% of phishing campaigns still require some form of human interaction, be that clicking on a link, downloading a file or opening an attachment. A figure that remains completely unchanged since the previous study in 2016!
The problem is that while security software and hardware firewalls are getting smarter and smarter, they still don’t catch 100% of the 3.4billion fake emails sent each day. Humans are still, unfortunately, far less effective at spotting and removing phishing emails.
Across our client-base during initial baseline tests, Phishing Tackle has noted around a 30% Click-Prone rate, representing an enormous threat surface across most organisations.
The key factor in the success of these email attacks is social engineering. With hackers going to great length in the process of making each new campaign more believable than the last.
The outlook may seem cloudy, but in fact it’s quite the opposite.
As more organisations implement effective security awareness training (SAT) into their staff policies, so the weakest link of the chain is strengthened. One of Phishing Tackle’s customers kindly allowed us to use one of their charts showing just how effective their simulated phishing and SAT campaign had been.
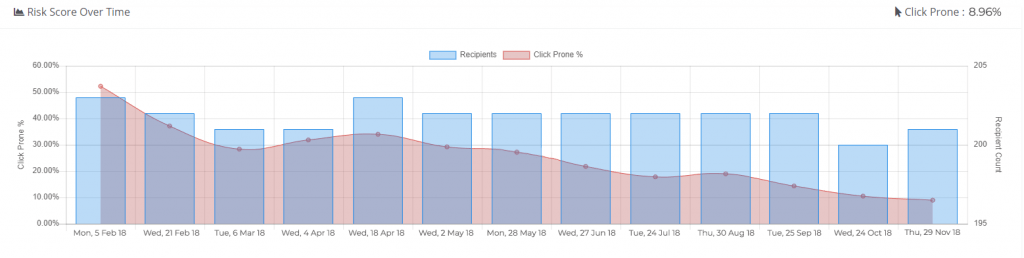
While 9% is still not ideal, a reduction from more than five times that amount of clickers shows excellent progress and an incredible reduction in organisation risk.
We implore all our readers to seek additional training, the fight against cyber crime is one that takes time, patience and regular work.
*Just in case I was not entirely clear, the hacking scene chosen was used in jest.








